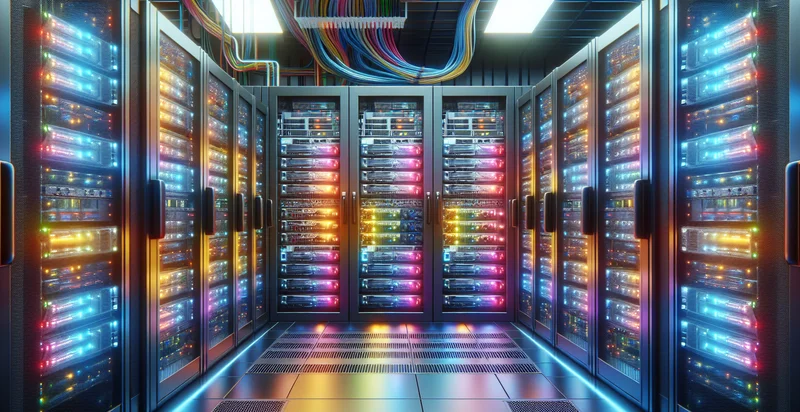
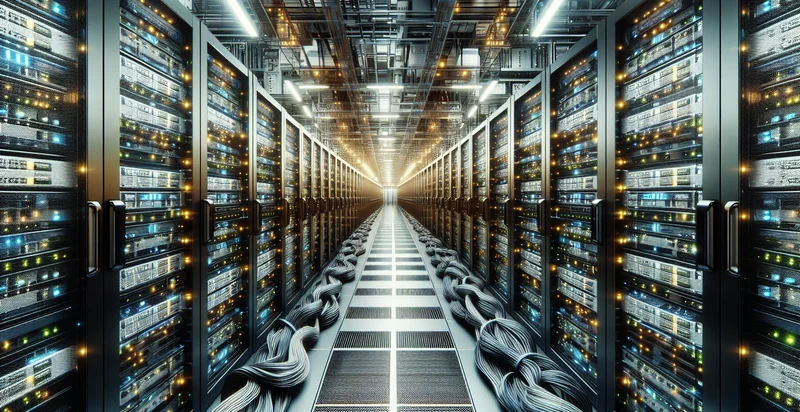
Identify if data center is unlocked
using AI
Below is a free classifier to identify if data center is unlocked. Just upload your image, and our AI will predict if the data center is unlocked - in just seconds.
Contact us for API access
Or, use Nyckel to build highly-accurate custom classifiers in just minutes. No PhD required.
Get started
import nyckel
credentials = nyckel.Credentials("YOUR_CLIENT_ID", "YOUR_CLIENT_SECRET")
nyckel.invoke("if-data-center-is-unlocked", "your_image_url", credentials)
fetch('https://www.nyckel.com/v1/functions/if-data-center-is-unlocked/invoke', {
method: 'POST',
headers: {
'Authorization': 'Bearer ' + 'YOUR_BEARER_TOKEN',
'Content-Type': 'application/json',
},
body: JSON.stringify(
{"data": "your_image_url"}
)
})
.then(response => response.json())
.then(data => console.log(data));
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: Bearer YOUR_BEARER_TOKEN" \
-d '{"data": "your_image_url"}' \
https://www.nyckel.com/v1/functions/if-data-center-is-unlocked/invoke
How this classifier works
To start, upload your image. Our AI tool will then predict if the data center is unlocked.
This pretrained image model uses a Nyckel-created dataset and has 2 labels, including Locked and Unlocked.
We'll also show a confidence score (the higher the number, the more confident the AI model is around if the data center is unlocked).
Whether you're just curious or building if data center is unlocked detection into your application, we hope our classifier proves helpful.
Related Classifiers
Need to identify if data center is unlocked at scale?
Get API or Zapier access to this classifier for free. It's perfect for:
- Access Control Monitoring: This use case focuses on enhancing security protocols by monitoring access to the data center. The identifier can trigger alerts whenever the data center is unlocked, allowing security personnel to respond promptly to unauthorized access attempts.
- Compliance Auditing: Organizations must comply with various regulations regarding data protection and access management. By logging instances of when the data center is unlocked, businesses can provide detailed reports for audits, demonstrating adherence to compliance requirements.
- Intrusion Detection: The identifier can be integrated with an intrusion detection system to enhance overall security. If the data center is unlocked outside of predetermined schedules, it can signal potential breaches, prompting immediate investigation.
- Employee Activity Tracking: Businesses can utilize this function to track employee access patterns within the data center. Analyzing this data can help improve operational efficiency and identify any unusual behavior that may require further review.
- Incident Response & Management: In the event of a security breach or incident, having a record of when the data center was unlocked can be critical. This information can assist in piecing together timelines and understanding the nature of the event for better incident response management.
- Maintenance Scheduling: The identifier can assist in planning and scheduling routine maintenance of data center equipment. By confirming when the center is accessible, facilities teams can optimize maintenance windows, reducing downtime and disruption.
- Risk Assessment & Security Review: Regularly evaluating how often the data center is unlocked can provide insights into security risks. By correlating these events with security incidents, businesses can bolster their security measures and reassess risk management strategies.